Technology
Understanding Vehicle Ownership and What You Can Legally Check in the UK

When people try to find a car owner by registration number, the intention is usually practical, checking who a vehicle belongs to before buying it, verifying a suspicious car, or understanding details after an incident. While it may seem like something that should be instantly available, the UK system is designed very differently.
Vehicle ownership data is protected under strict privacy regulations, meaning personal details of the registered keeper are not publicly accessible. However, that doesn’t mean you are left without options. Instead, what you can access is structured vehicle intelligence that helps you understand a car’s background, condition, and risk level.
This is where platforms like The Auto Experts play an important role, turning complex DVLA-linked data into clear, usable insights for everyday users.
Why direct access to car owner details is restricted in the UK
Many assume that entering a registration number should instantly reveal the current owner, but UK law prevents this level of access.
The DVLA holds all registered keeper information securely and only releases it under specific legal circumstances such as insurance investigations, police enquiries, or court-approved requests. For general users, this means personal identity details like name and address are not available through a simple lookup.
What is important to understand is that this restriction is not a limitation in value, but a shift in focus. Instead of revealing who owns the vehicle, the system is designed to help users understand how the vehicle has been used over time.
This is why a modern vehicle registration lookup is far more useful when it focuses on:
- Ownership change patterns over time
- Registration plate consistency
- Number of previous keepers
- Vehicle identity verification
These insights often provide a clearer and more reliable picture of a vehicle’s background than simply knowing the current registered keeper.
To understand how these registration-based insights work in practice and what can be legally accessed, you can refer to this detailed guide on how to find a car owner.
This guide explains the practical limitations and helps users understand what a DVLA vehicle check can realistically reveal.
What information can you actually get from a registration number?
Instead of revealing personal ownership details, a registration number unlocks structured vehicle data that helps you assess the condition and reliability of a car.
A proper approach to understanding how to find a vehicle owner today is less about identity and more about trust and risk evaluation. When a vehicle is checked properly, you can often identify patterns that matter far more than who currently owns it.
For example, frequent ownership changes in a short period may indicate unresolved issues, while stable ownership often suggests better maintenance and care. Similarly, inconsistencies in registration history can sometimes highlight potential concerns such as plate changes or data mismatches.
This is especially relevant in the used car market, where vehicles may look visually perfect but still carry hidden risks like finance obligations, mileage discrepancies, or previous insurance write-offs.
To get a complete understanding of a vehicle’s background in one place, you can explore The Auto Experts platform by using a vehicle history check.
Their reports bring together multiple data sources into a single, easy-to-understand format so users can make informed decisions without relying solely on seller information.
How DVLA-based checks help improve buying decisions
A modern DVLA owner check is not about revealing private information, it is about reducing uncertainty when buying or evaluating a vehicle.
When ownership data is analysed alongside vehicle history, it helps build a clearer picture of how the car has been treated over its lifetime. For instance, a vehicle that has passed through several owners in a short time may require closer inspection, while long-term ownership can often indicate stability and consistent maintenance.
What makes these checks especially valuable is how they combine ownership patterns with other important indicators such as MOT history, mileage consistency, insurance write-off status, and theft or export flags.
Together, these factors help shift decision-making from guesswork to evidence-based evaluation.
This is particularly useful in today’s used car market, where prices vary widely and listings move quickly. Buyers who rely only on appearance or seller claims often miss important warning signs that a proper data check would reveal instantly.
Why vehicle history is more important than ownership identity
While many users start with the goal of identifying a registered keeper, the real value lies in understanding the vehicle’s past.
A car’s history often reveals more about its long-term reliability than any single ownership record. Vehicles that have changed hands frequently may have underlying mechanical or financial issues that are not immediately visible during inspection.
Similarly, inconsistencies in records or gaps in data can sometimes indicate risks such as cloning, undeclared damage, or incorrect documentation. These are issues that cannot be detected through a visual check alone.
This is why experienced buyers, dealers, and inspectors rely more on structured vehicle reports than on ownership identity. It helps remove emotional bias and replaces it with factual clarity.
In a market where quick decisions are common, having access to verified vehicle data significantly reduces the risk of overpaying or buying a problematic car.
Final Thoughts
Although it is not possible to directly access personal ownership details through a registration number, you can still gain meaningful insight into a vehicle’s background and reliability.
Whether you are trying to understand car ownership history, performing a car owner check, or using a DVLA owner check, the goal is always the same: making safer and more informed decisions before buying or verifying a vehicle.
With platforms like The Auto Experts, users gain access to structured vehicle intelligence that transforms complex DVLA data into practical, easy-to-read insights that support confident buying choices.
FAQs
1. Can I find out the name of a car owner using a registration number?
No, personal owner details are protected under UK data privacy laws and are not publicly accessible.
2. What is the main purpose of a car owner check?
It helps users understand ownership history, number of previous keepers, and vehicle background details.
3. Is a DVLA owner check useful for used car buyers?
Yes, it helps identify ownership patterns and potential risks that may not be visible during inspection.
4. What is more important than knowing the car owner’s identity?
Understanding the vehicle’s history, condition, and risk indicators is far more important for making a safe purchase decision.
Technology
What Is Sruffer DB? Inside the Next-Generation Hybrid Database System
Sruffer DB is described as a next-generation database management system made for modern digital workloads. It is built to combine the strong structure of SQL databases with the flexible nature of NoSQL systems. This means it can handle tables, JSON documents, logs, event streams, and other types of data in one place. For teams that work with fast-moving information, this can reduce the need for many separate tools.
The main idea behind Sruffer DB is simple. Modern businesses do not use only one type of data anymore. A company may store customer records in tables, product details in JSON, system logs in unstructured formats, and real-time activity in event streams. Sruffer DB aims to bring all these data types together inside one unified database engine.
Quick Facts
| Detail | Information |
|---|---|
| Name | Sruffer DB |
| Type | Hybrid SQL-NoSQL Database Management System |
| Category | Modern DBMS |
| Main Focus | Real-Time Data Processing |
| Core Strength | SQL Reliability with NoSQL Flexibility |
| Data Support | Structured, Semi-Structured, and Unstructured Data |
| Key Feature | Hybrid Transactional and Analytical Processing |
| Best For | Developers, Startups, and Enterprise Teams |
| Use Cases | Analytics, Logs, Events, Dashboards, Fraud Detection |
| Scalability | Horizontal and Vertical Scaling |
| Security | Encryption and Access Controls |
| Interface | User-Friendly Data Management Tools |
| Main Benefit | Faster Data Handling in One Unified Engine |
| Target Market | Modern Apps, Cloud Platforms, and Fast-Growing Businesses |
Why Sruffer DB Matters Today?
The way businesses use data has changed very quickly. In the past, many companies only needed a simple relational database to store customer names, orders, invoices, and reports. Today, applications collect huge amounts of information every second. This data comes from websites, mobile apps, sensors, payment systems, search tools, social platforms, and cloud services.
Sruffer DB matters because it is designed for this new type of workload. It does not treat data as one simple format. Instead, it supports structured, semi-structured, and unstructured information together. This helps teams build faster systems without moving data between too many platforms.
For growing companies, this can be a major advantage. A startup may begin with a small app but quickly grow into a platform with millions of users. If its database cannot scale or process data in real time, the business may face slow performance and technical problems. Sruffer DB aims to solve that problem by offering speed, scaling, and flexibility from the start.
Hybrid SQL and NoSQL Design
One of the strongest parts of Sruffer DB is its hybrid SQL and NoSQL design. SQL databases are popular because they are reliable, structured, and trusted for important transactions. They are often used in finance, healthcare, business software, and any system where accuracy is very important. NoSQL databases are popular because they are flexible and can store changing data formats like JSON documents.
Sruffer DB tries to combine both worlds. It gives developers the structure and trust of SQL while also giving them the freedom of NoSQL. This helps teams avoid choosing one system and losing the benefits of the other. For example, a company can manage order records in tables while storing flexible customer preferences as JSON documents.
This hybrid model is useful because modern applications rarely stay simple. A business may begin with basic records, then later add analytics, logs, search data, user behavior, and live dashboards. With Sruffer DB, these different data needs can be managed in a more connected way.
Structured, Semi-Structured, and Unstructured Data
Sruffer DB is designed to work with many kinds of data. Structured data includes rows and columns, such as customer records, product lists, banking transactions, and inventory tables. This type of data is easy to organize and query. It is still very important for business systems that need clear rules and strong accuracy.
Semi-structured data includes JSON documents, API responses, flexible product details, user settings, and content records. This data does not always fit perfectly into tables. Many modern apps use JSON because it is flexible and easy for developers to work with. Sruffer DB supports this style so teams can store flexible information without forcing it into a rigid format.
Unstructured data includes logs, media metadata, event records, system messages, and other information that does not follow a fixed structure. This type of data is growing fast because apps now generate constant activity records. Sruffer DB helps manage this data along with traditional records, making it easier to analyze the full picture of a business.
Real-Time Analytics
Real-time analytics is one of the most important features linked with Sruffer DB. Many older systems require data to be moved from an operational database into a separate analytics tool before reports can be created. This process can take time and may cause delays. In fast industries, even a small delay can affect decisions.
Sruffer DB is designed to support analytics on live data. This means users can track behavior, patterns, risks, and performance as events happen. A business can monitor sales activity, customer actions, system errors, or payment behavior without waiting for a separate reporting process.
This is valuable for companies that depend on instant decisions. A finance company can detect possible fraud faster. A retail platform can track stock movement in real time. A content team can study search trends quickly. Sruffer DB helps turn live data into useful insight without slowing down the main application.
HTAP Capabilities
Sruffer DB supports the idea of Hybrid Transactional and Analytical Processing, also known as HTAP. This means the database can handle normal transactions and analytical queries in the same system. Transactions include actions like saving an order, updating a customer profile, recording a payment, or changing inventory levels.
Analytics includes deeper questions, such as which products are selling fastest, which users are most active, or which transactions look risky. In many traditional setups, these two workloads are separated. One database handles transactions, while another system handles analytics. This can make infrastructure more complex.
With HTAP, Sruffer DB aims to reduce that complexity. Teams can process daily business activity and study that activity at the same time. This makes the system more useful for dashboards, monitoring tools, reporting systems, and AI-powered applications that need fresh data.
Speed and Performance
Performance is a major reason why businesses look for modern database systems. A slow database can hurt the user experience, increase costs, and make applications harder to scale. Sruffer DB focuses on low latency and high-speed query processing, especially for complex workloads.
The system is designed to handle both fast reads and reliable writes. This is important for apps that need to save data quickly while also returning results instantly. For example, a live dashboard should update without delay, but the same system must also keep records accurate and safe.
Sruffer DB’s unified engine is meant to reduce the need for data movement between tools. Less movement can mean faster results and fewer points of failure. When data stays closer to where it is processed, teams can build faster workflows and improve application performance.
Scalability for Modern Applications
Modern applications must be ready to grow. A small platform can suddenly receive more users, more traffic, and more data than expected. If the database cannot scale, the app may slow down or fail. Sruffer DB is built with scalability in mind, supporting both horizontal and vertical growth.
Horizontal scaling means adding more machines or nodes to spread the workload. This is useful for cloud-native systems and large applications. Vertical scaling means increasing the power of existing servers by adding more CPU, memory, or storage. Both approaches are important because different businesses grow in different ways.
For startups, scalability is especially important. They may not know how fast their product will grow. Sruffer DB gives them a database model that can start small and expand as needed. For enterprises, scalability helps manage large data volumes, global users, and demanding analytics workloads.
Cloud-Native Architecture
Sruffer DB is designed for cloud-native environments. This means it can fit into modern cloud platforms, distributed systems, and flexible infrastructure models. Cloud-native databases are important because many businesses no longer depend only on traditional on-premise servers.
A cloud-native database should be easy to deploy, scale, monitor, and maintain. Sruffer DB is positioned as a system that can support these needs. It can help teams build applications that run across cloud environments while still handling complex data interactions.
This makes Sruffer DB useful for SaaS platforms, mobile applications, AI tools, e-commerce systems, and enterprise software. As more businesses move to the cloud, databases must support flexible deployment and strong performance. Sruffer DB is built around that modern requirement.
Security and Compliance
Security is a key part of any database system. Sruffer DB includes enterprise-focused security features such as encryption and access controls. Encryption helps protect data when it is stored or moved. Access controls help decide who can view, edit, or manage specific information.
This is important for industries that handle private or sensitive data. Healthcare companies manage patient records. Finance companies process payments and fraud signals. Retail businesses store customer details and purchase history. In all these cases, weak security can create serious risks.
Sruffer DB’s security model is designed to support modern business needs. While every organization must still manage its own compliance rules, a database with built-in security tools can make that process easier. Strong permissions, protected storage, and controlled access help businesses keep data safer.
Developer-Friendly Interface
Sruffer DB is also described as a developer-focused platform. Many database systems become difficult to manage when applications grow. Developers may need to write complex queries, move data between systems, and maintain several tools at once. Sruffer DB aims to simplify this experience.
Its user-friendly interface is meant to help teams manage complex data interactions more easily. Developers can work with different types of data inside one system instead of switching between separate databases. This can improve productivity and reduce confusion.
A good developer experience matters because it affects how fast teams can build and improve products. If a database is hard to use, projects slow down. If it is clear, flexible, and powerful, developers can focus more on building useful features.
Sruffer DB for Startups
Startups often need tools that are fast, flexible, and affordable to manage. They usually do not have large engineering teams at the beginning. This makes simple architecture very important. Sruffer DB can be useful because it combines several database capabilities into one system.
A startup may need user accounts, payment records, analytics, logs, and product data from the first stage of growth. Using separate systems for each need can become expensive and confusing. Sruffer DB helps reduce this problem by supporting multiple workloads in one place.
As the startup grows, the same database approach can support more users and larger datasets. This makes Sruffer DB attractive for teams that want to avoid early technical limits. It gives them room to build, test, and scale without changing the full data system too soon.
Enterprise Use Cases
Enterprise teams often work with large systems, strict security needs, and complex data flows. Sruffer DB is designed to support these environments by offering performance, scalability, and multi-model data handling. Large companies need databases that can manage transactions, analytics, logs, and operational data together.
In healthcare, Sruffer DB can support patient records, appointment systems, and monitoring data. In finance, it can help with transaction tracking, fraud detection, and real-time reporting. In retail, it can support inventory updates, customer behavior analysis, and sales dashboards.
Enterprise teams also care about reliability. A database must keep data consistent while still supporting fast queries. Sruffer DB’s hybrid model aims to deliver both. This makes it useful for businesses that need one system to support many departments and workflows.
SEO and Content Strategy Uses
Sruffer DB can also be used in SEO and content strategy environments. Modern SEO depends heavily on data. Businesses track keywords, rankings, user behavior, search patterns, content performance, and competitor activity. This information can change quickly, so real-time analysis is valuable.
A content platform could use Sruffer DB to store keyword data in tables, user behavior in event streams, and article metadata in flexible documents. This allows teams to study performance from different angles. They can see which topics are growing, which pages need updates, and which search terms are bringing traffic.
For publishers and agencies, this can improve decision-making. Instead of waiting for slow reports, they can use live data to adjust strategy faster. Sruffer DB’s ability to process mixed data types makes it useful for content teams that want a more data-driven SEO workflow.
Main Benefits of Sruffer DB
The biggest benefit of Sruffer DB is its unified design. Instead of using one database for structured records, another for JSON data, another for logs, and another for analytics, teams can manage many of these needs in one platform. This can reduce complexity and improve speed.
Another major benefit is real-time insight. Businesses today cannot always wait hours or days to understand what is happening. Sruffer DB helps teams analyze live data and act faster. This is useful in fraud detection, inventory tracking, monitoring, search analysis, and customer behavior systems.
Sruffer DB also supports growth. Its scaling model helps applications expand as data and traffic increase. For modern companies, this is essential. A database must not only work today. It must also be ready for tomorrow’s users, features, and business demands.
Challenges to Consider
Even though Sruffer DB offers many benefits, businesses should also understand the possible challenges. Hybrid systems can be powerful, but they may require careful planning. Teams need to understand how to organize data, manage workloads, and tune performance properly.
Another challenge is adoption. If a company already uses older SQL or NoSQL systems, moving to a new hybrid platform may take time. Data migration, staff training, and integration with existing tools must be handled carefully. A strong migration plan is important.
Newer systems may also have smaller communities than long-established database platforms. This means businesses should review documentation, support options, and ecosystem maturity before using Sruffer DB for critical workloads. Good planning can help reduce these risks.
Future of Sruffer DB
The future of Sruffer DB looks connected to the larger future of hybrid databases. Businesses are moving toward systems that can do more with less complexity. They want fewer tools, faster analytics, better security, and easier scaling. Sruffer DB fits this direction.
As AI, automation, cloud apps, and real-time platforms grow, databases will need to process more data at higher speed. Sruffer DB’s multi-model and HTAP approach makes it suitable for this type of future. It can support live analytics, flexible data storage, and fast application development.
If Sruffer DB continues to improve its ecosystem, developer tools, and enterprise features, it could become a strong choice for companies that need modern data infrastructure. Its biggest promise is simple: one flexible database engine for the complex data needs of modern businesses.
Final Thoughts
Sruffer DB is described as a powerful next-generation database system built for the modern age of data. It combines SQL structure, NoSQL flexibility, real-time analytics, cloud scalability, and enterprise security into one platform. This makes it useful for developers, startups, and large businesses that need to manage fast-growing data.
Its hybrid approach is the main reason it stands out. Instead of forcing teams to choose between relational tables and flexible documents, Sruffer DB supports both. It also helps reduce delays by allowing analytics and transactions to run together in one system.
For companies that need speed, flexibility, and future-ready infrastructure, Sruffer DB offers a strong vision. It is designed for the way modern applications work today and the way data systems are likely to grow in the future.
FAQs
What is Sruffer DB?
Sruffer DB is a modern hybrid SQL-NoSQL database management system. It is designed to handle structured data, JSON documents, logs, event streams, and real-time analytics in one unified engine.
Is Sruffer DB a SQL or NoSQL database?
Sruffer DB is both. It combines SQL-style structure with NoSQL flexibility. This allows users to manage traditional tables and flexible document data inside the same system.
What is Sruffer DB used for?
Sruffer DB can be used for real-time analytics, live dashboards, fraud detection, inventory tracking, event streaming, SEO data analysis, customer behavior tracking, and enterprise data management.
Who should use Sruffer DB?
Sruffer DB is useful for developers, startups, SaaS companies, enterprise engineering teams, and businesses that manage large or fast-moving datasets across different formats.
Why is Sruffer DB important for modern applications?
Sruffer DB is important because modern apps need speed, flexibility, scalability, and real-time insight. It helps teams manage many types of data without relying on many separate database systems.
Technology
What Is Face Zem? The Complete Guide to AI Facial Recognition Technology

Face Zem is an advanced AI-powered facial recognition technology designed to identify and verify people in real time using computer vision and biometric analysis. The system studies facial structures, converts them into digital signatures, and compares them with stored databases to confirm identities within seconds. Unlike traditional security systems that rely on passwords, ID cards, or fingerprints, Face Zem uses the human face as the primary authentication method.
The growing popularity of AI facial recognition technology has made systems like Face Zem extremely important across many industries. Businesses, governments, banks, hospitals, and security organizations are adopting these systems because they provide faster verification, stronger security, and improved automation. As artificial intelligence continues to evolve, facial recognition technology is becoming smarter, more accurate, and more reliable in both personal and professional environments.
Quick Summary
| Feature | Details |
|---|---|
| Technology Name | Face Zem |
| Type | AI Facial Recognition Technology |
| Main Purpose | Real-Time Identity Verification |
| Core Technologies | AI, Deep Learning, Computer Vision |
| Recognition Method | Biometric Face Mapping |
| Accuracy Level | Up to 99.7% |
| Processing Speed | Under 0.2 Seconds |
| Security Features | Liveness Detection & Anti-Spoofing |
| Main Industries | Security, Banking, Retail, Healthcare |
| Hardware Support | ARM NPUs & AI Processors |
| Data Protection | Anonymous Faceprints |
| Detection Capability | Real-Time Facial Analysis |
| Environmental Support | Low Light & Outdoor Recognition |
| Key Benefit | Fast Contactless Authentication |
| Future Potential | Smart Cities & Digital Identity |
How Face Zem Technology Works?
Face Zem operates through several intelligent AI-driven processes that allow the system to recognize a person almost instantly. The process starts when a camera captures a live image or video feed. The AI software first detects the presence of a human face within the frame before beginning deeper facial analysis. This step is known as face detection and acts as the foundation of the entire recognition process.
After detecting the face, the system begins feature extraction. During this stage, Face Zem analyzes important facial landmarks such as the distance between the eyes, nose width, jawline contour, cheekbone structure, forehead shape, and lip position. These measurements are converted into a unique mathematical code called a faceprint or facial signature. The system then compares this code against stored records inside secure databases to find a matching identity in real time.
The Role of Artificial Intelligence in Face Zem
Artificial intelligence is the core engine that powers Face Zem. Without AI and machine learning, facial recognition systems would struggle to deliver accurate and reliable results under changing conditions. Modern AI allows the system to learn from millions of facial images, helping it improve recognition accuracy over time. The technology becomes smarter with continued usage because deep learning models constantly refine their understanding of facial structures and patterns.
AI also allows Face Zem to recognize people under difficult conditions. The system can identify faces even when users wear glasses, hats, masks, or have changes in facial hair. It can also adapt to different camera angles and lighting conditions. This flexibility is one of the main reasons why Face Zem is considered a major improvement over older biometric systems that relied only on simple two-dimensional image analysis.
Deep Learning and CNN Facial Recognition
Modern Face Zem systems rely heavily on deep learning models and Convolutional Neural Networks, commonly known as CNNs. These neural networks are designed specifically for image analysis and facial recognition tasks. CNN technology studies facial images layer by layer, identifying patterns, textures, edges, and unique structural details before combining them into a complete identity profile.
This advanced method allows Face Zem to reach accuracy levels of up to 99.7% in many conditions. Deep learning systems are far more advanced than traditional software because they can continue improving through training and large-scale data analysis. The AI can learn subtle facial variations that human observers may never notice, making the system highly effective for security, authentication, and identity management purposes.
Real-Time Facial Recognition Capabilities
One of the biggest advantages of Face Zem is its ability to perform real-time facial recognition. The system can process live camera feeds and identify individuals almost instantly while they move through checkpoints, offices, airports, or public spaces. This capability is especially useful in crowded areas where fast identification is necessary for both safety and operational efficiency.
The speed of Face Zem is powered by dedicated AI hardware such as Neural Processing Units and ARM-based processors. These components are specifically designed for fast AI calculations and image processing. Some advanced systems can process thousands of registered users in less than 0.2 seconds, making the technology ideal for large-scale operations where delays are unacceptable.
Advanced 3D Facial Mapping
Older facial recognition systems mostly depended on flat 2D images, which limited their accuracy and security. Face Zem improves this process using advanced 3D facial mapping technology. Instead of relying only on visible facial features, the system analyzes depth, facial curves, and structural measurements to create highly accurate biometric models.
Many modern systems scan over 30,000 invisible infrared points across the human face to generate detailed facial maps. These nodal points help the AI identify even tiny differences between faces. This technology makes it extremely difficult for criminals to bypass the system using printed photographs, video recordings, or fake masks because the AI can detect depth and real facial structure.
Liveness Detection and Anti-Spoofing Protection
Liveness detection is one of the most important security features included in Face Zem systems. Cybercriminals often attempt to trick facial recognition systems using photographs, digital screens, or realistic masks. Face Zem uses advanced anti-spoofing technology to ensure the person standing in front of the camera is a real human being.
The system checks for natural facial movement, blinking, skin texture, heat signatures, and depth patterns. Many advanced versions use dual-camera systems with infrared sensors to improve detection accuracy. These features greatly reduce identity theft risks and increase trust in AI-powered biometric authentication systems used in banking, airports, government facilities, and secure workplaces.
Face Zem in Security and Access Control
Security and access control are among the biggest applications of Face Zem technology. Businesses and organizations are replacing traditional passwords, ID cards, and fingerprint scanners with AI-powered facial recognition systems because they are faster, safer, and easier to use. Employees can enter offices or restricted areas simply by looking at a camera for a few seconds.
Government facilities, airports, hotels, and smart residential buildings also use Face Zem to improve security operations. Real-time identity verification helps prevent unauthorized access while reducing the need for physical contact. The technology also creates digital records of entry and exit activity, helping organizations improve monitoring and security management.
Banking and Financial Industry Applications
Banks and fintech companies are rapidly adopting Face Zem technology to strengthen fraud prevention and digital identity verification. Facial recognition systems allow customers to verify themselves remotely through smartphones or webcams without visiting physical branches. This makes online banking safer and more convenient for users worldwide.
Face Zem is also used for high-value transaction approval and suspicious activity monitoring. If the AI detects unusual behavior or facial mismatches during authentication, security alerts can be triggered instantly. These features help financial institutions reduce fraud, identity theft, and account hacking attempts while improving customer trust in digital banking systems.
Face Zem in Healthcare Systems
Healthcare organizations are increasingly using Face Zem technology to improve patient management and medical security. Hospitals and clinics use facial recognition for patient registration, staff access control, and secure handling of medical records. This reduces paperwork, speeds up check-in procedures, and minimizes identity-related errors.
Researchers are also exploring how AI facial analysis could help identify certain genetic conditions and neurological disorders through facial symmetry and movement patterns. Although this field is still developing, it demonstrates how facial recognition technology may expand beyond security and become a valuable healthcare support tool in the future.
Smart Retail and Customer Experience
Retail businesses are using Face Zem to better understand customer behavior and improve shopping experiences. AI-powered systems can analyze customer traffic, dwell time, repeat visits, and shopping habits. Loyalty program members can receive more personalized services through automatic recognition systems integrated into smart retail platforms.
Retail security also benefits from facial recognition technology. Stores can monitor suspicious behavior and reduce theft more efficiently. At the same time, businesses gain valuable customer insights that help improve store layouts, product placement, and overall customer satisfaction. This combination of analytics and security makes Face Zem highly valuable for modern retail environments.
Public Safety and Smart City Integration
Face Zem is playing a major role in smart city development projects around the world. Cities are integrating AI-powered surveillance systems into transportation hubs, public streets, stadiums, airports, and large event venues. These systems help improve emergency response times, monitor public safety, and identify persons of interest in crowded areas.
Large public venues can use watchlist systems that automatically alert security teams when specific individuals are detected. Smart city networks combine facial recognition with cloud computing, traffic systems, and intelligent cameras to create connected security environments capable of real-time monitoring and analysis across entire urban areas.
Environmental Adaptation and Low-Light Recognition
One of the biggest improvements in Face Zem technology is its ability to function under difficult environmental conditions. Older facial recognition systems often failed in poor lighting, bright sunlight, or crowded environments. Modern Face Zem systems solve these problems using Wide Dynamic Range technology, infrared lighting, and adaptive AI image processing.
The system can recognize people in low-light areas, outdoor environments, and changing weather conditions. It can also identify partially covered faces, including individuals wearing masks, sunglasses, or hats. This environmental flexibility makes Face Zem reliable for both indoor and outdoor security applications where lighting and visibility constantly change.
Privacy Concerns and Ethical Challenges
Although Face Zem offers many advantages, it also raises important privacy and ethical concerns. Facial data is considered highly sensitive because it represents permanent biometric information tied directly to personal identity. Many people worry about mass surveillance, unauthorized tracking, and misuse of facial recognition databases.
To address these concerns, many modern facial recognition companies now follow privacy-by-design principles. Instead of storing raw photos, systems convert facial images into encrypted mathematical signatures that cannot easily recreate the original face. Governments and technology companies are also developing stricter rules for biometric data protection, consent management, and responsible AI usage.
The Future of Face Zem Technology
The future of Face Zem looks extremely promising as artificial intelligence continues advancing at a rapid pace. Future systems are expected to become even faster, smarter, and more accurate. Researchers are developing AI models capable of emotion detection, behavior prediction, voice-and-face authentication, and advanced deepfake detection systems.
Face Zem may eventually become a central part of digital identity systems used in smart homes, autonomous vehicles, schools, airports, hospitals, and government services. As AI hardware improves and biometric technologies become more secure, facial recognition is expected to play a major role in the future of global security and digital interaction.
Why Face Zem Is Changing Modern Technology?
Face Zem represents a major transformation in the way humans interact with security and identity systems. Instead of relying on passwords, ID cards, or physical keys, facial recognition provides fast, contactless, and highly secure authentication powered by artificial intelligence. Businesses benefit from greater efficiency, while users enjoy smoother and more convenient experiences.
Although privacy concerns remain important, improvements in encryption, anonymous faceprints, and ethical AI practices are helping make biometric systems safer and more trustworthy. As adoption continues growing across industries, Face Zem is likely to become one of the most influential AI technologies shaping the future of security, automation, and digital identity management.
FAQs
What is Face Zem?
Face Zem is an AI-powered facial recognition technology that uses computer vision and deep learning to identify and verify people through biometric facial analysis in real time.
How accurate is Face Zem technology?
Modern Face Zem systems can achieve accuracy levels of up to 99.7% by using advanced deep learning, CNN models, and 3D facial mapping technology.
Where is Face Zem commonly used?
Face Zem is widely used in security systems, banking, healthcare, retail stores, airports, smart cities, employee attendance systems, and government facilities.
What is liveness detection in Face Zem?
Liveness detection is an anti-spoofing security feature that checks whether the subject is a real human instead of a photograph, video, or mask.
Is Face Zem safe for privacy and security?
Many modern Face Zem systems protect privacy by storing encrypted mathematical faceprints instead of raw facial images, helping reduce the risk of identity theft and database misuse.
Technology
iPhone Locked to Owner? How to Remove iCloud Activation Lock (2026 Guide)

Buying a used iPhone can save money, but there’s one problem that still catches a lot of people off guard, which is the dreaded “iPhone Locked to Owner” screen. Once this message appears, the device becomes unusable until the original Apple ID credentials are entered. This security system is called iCloud Activation Lock, and while it’s great for preventing theft, it can also create problems for legitimate users.
In this guide, we’ll go through the most effective ways to remove iCloud Activation Lock in 2026, including official methods, practical iPhone unlocker alternatives, and what actually works in real world situations.
What Is iCloud Activation Lock?
Activation Lock is part of Apple’s Find My feature. When Find My iPhone is enabled, the device becomes linked to the owner’s Apple ID. Even after a factory reset, the iPhone still asks for the original account credentials before setup can continue. You’ll usually see this happen when:
- Buying a second-hand iPhone
- Forgetting Apple ID credentials
- Resetting an old device without signing out
- Receiving a locked device from someone else
Can iCloud Activation Lock Be Removed?
Yes, but the method depends on your situation. If you still have access to the Apple ID, the process is relatively simple. If not, your options become more limited. Generally, there are four realistic approaches:
- Reset the Apple ID password
- Ask the previous owner to remove the device
- Contact Apple Support
- Use specialized iPhone unlocker software
Let’s break them down one by one.
Method 1: Reset the Apple ID Password
If the device belongs to you and you simply forgot the password, this should always be your first option.
Step 1: Go to Apple’s password recovery page
Step 2: Enter your Apple ID
Step 3: Verify your identity
Step 4: Create a new password
Step 5: Return to the iPhone and sign in
This is the safest and most complete solution because the iPhone remains fully functional afterward.
Method 2: Ask the Previous Owner to Remove the Device
If you bought the iPhone from someone else, contact them if possible. They can remotely remove the Activation Lock through iCloud. Steps for the previous owner are as follows.
Step 1: Sign into iCloud and open Find My
Step 2: Select the iPhone
Step 3: Click Erase iPhone and Remove from Account
Once completed, restart the iPhone and continue setup normally.
Method 3: Use Apple Support
Apple may help remove Activation Lock if you can prove ownership. Usually, you’ll need original receipt, Serial number or IMEI, and valid identification.
Without proof of ownership, Apple typically won’t unlock the device.
Method 4: Use an iPhone Unlocking Tool
When the Apple ID is unavailable and contacting the previous owner isn’t possible, many users turn to dedicated unlocking software.
One commonly used option is MagFone iPhone Unlocker, which is designed to help users remove different types of iPhone locks, including Activation Lock in supported scenarios. It is a great option when you are looking for how to remove Apple ID from iPhone. Compared to manual methods, the process is usually much simpler for beginners.
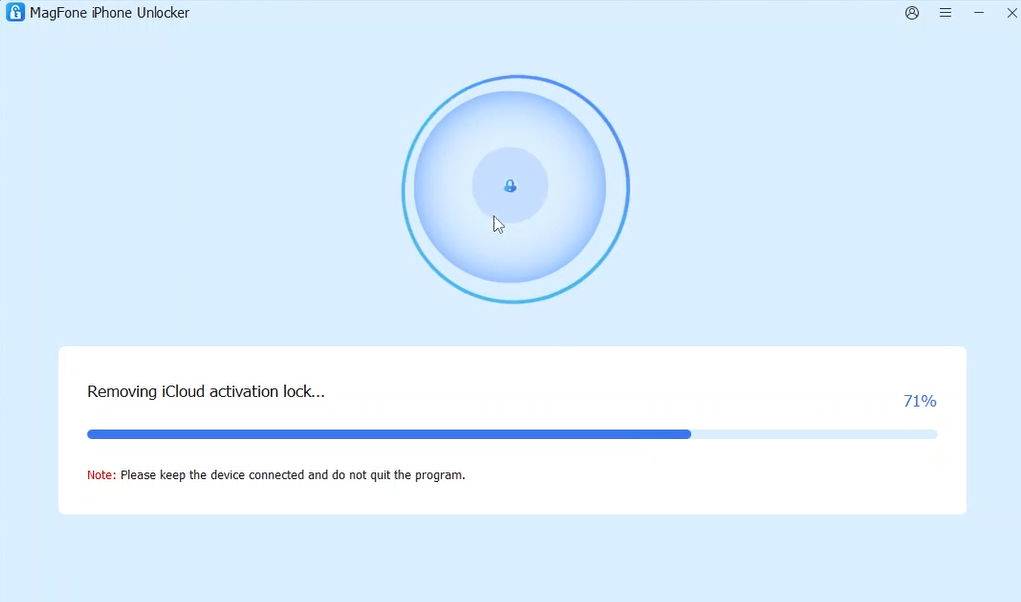
How to Remove iCloud Activation Lock Using MagFone iPhone Unlocker
If you’re stuck on the “iPhone Locked to Owner” screen and need a computer-based solution, here’s how the process generally works.
Step 1: Download and install MagFone iPhone Unlocker on your computer. Use a USB cable to connect the locked iPhone.
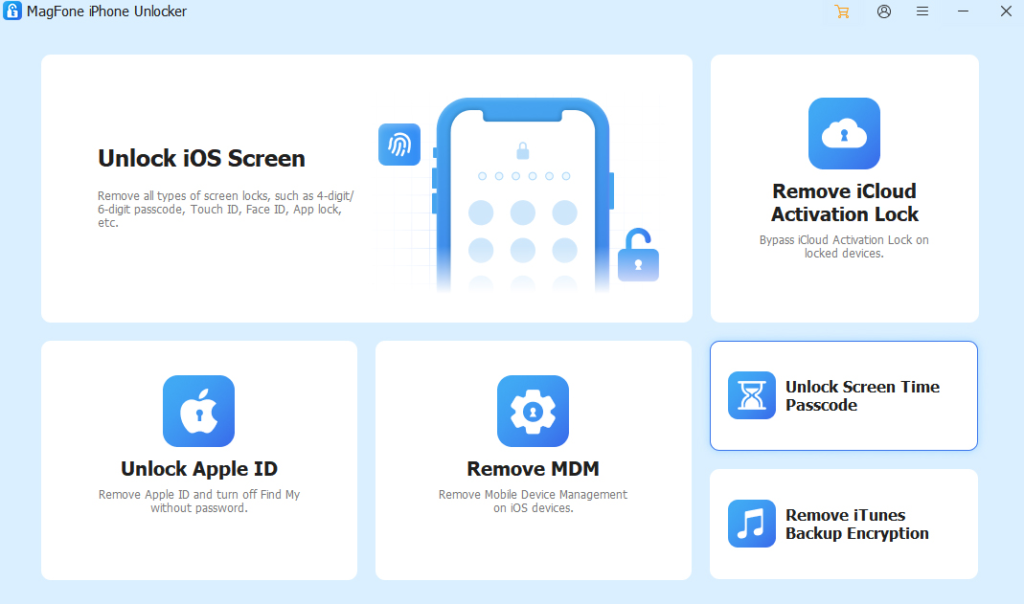
Step 2: Select Remove iCloud Activation Lock from the main interface. Follow the on-screen instructions to enter Recovery and DFU mode.
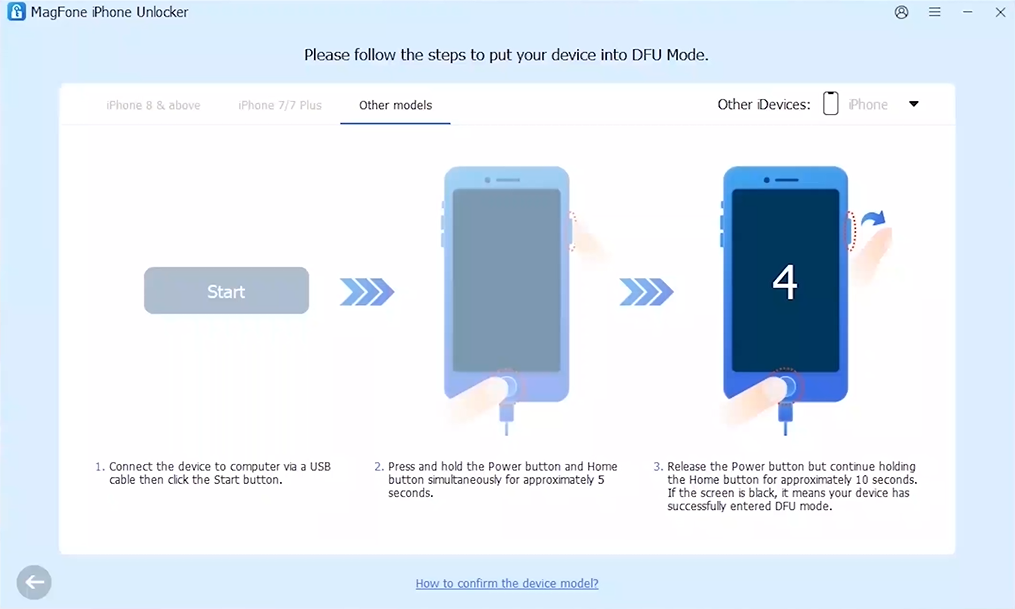
Step 3: The software will begin bypassing iCloud activation lock automatically. Once completed, the iPhone will restart and can be set up again.
Is It Safe?
Generally, yes, if you use trusted software like MagFone iPhone Unlocker and official downloads. Avoid suspicious “free bypass” tools online, as many are outdated, unreliable, or potentially unsafe.
FAQs
- Can iCloud Activation Lock really be removed?
In some situations, yes. The best method depends on whether you still have access to the original Apple ID.
- Can I remove Activation Lock without a computer?
Usually no. Most practical methods require a computer.
- Is bypassing Activation Lock legal?
Only on devices you legally own.
Final Thoughts
Activation Lock is designed to protect iPhones, but it can also become a headache for legitimate users. The best solution is always the official route, recovering the Apple ID or contacting the previous owner. But when those options aren’t available, tools like MagFone iPhone Unlocker can provide a more practical alternative for supported devices. The key is understanding your specific situation and choosing the method that actually fits it.
-

 Celebrity6 months ago
Celebrity6 months agoNancy Hallam: The Inspiring Life, Career, and Success Story Behind Ian Wright’s Wife
-

 Celebrity7 months ago
Celebrity7 months agoJohnny Carell: Inside the Life, Family, and Rising Success of Steve Carell’s Son
-

 Celebrity6 months ago
Celebrity6 months agoWho Is Maisie Mae Roffey? The Private Life, Family Story, and Quiet Success of Julie Walters’ Daughter
-

 Health4 months ago
Health4 months agoEnclomimed 25 (Enclomiphene) – Effective PCT Protocol
-

 Celebrity4 months ago
Celebrity4 months agoWho Is Cameron Kade Hickenbottom? Shawn Michaels’ Son and His Independent Creative Legacy
-
 Celebrity3 months ago
Celebrity3 months agoWho Is Mark Gero? Inside the Life, Art, and Quiet Legacy of an American Creative
-

 Celebrity5 months ago
Celebrity5 months agoMeet Nancy Strang: The Inspiring Life, Success Story, and Legacy of Louis Theroux’s Wife
-

 Business5 months ago
Business5 months agoSimon Dixon Biography: Lifestyle, Net Worth, Family, Career and Success Story





